Most of you do not know this. Biometrics — the use of your physical and behavioral traits for identification — has moved far beyond the familiar fingerprint scanner on your phone.
Today, technology is capturing and analyzing deeply personal, unique characteristics like the way you talk, the way you move, and even the subtle patterns in your blood vessels. This evolution offers unprecedented convenience and security, but it also introduces profound risks to privacy that every individual needs to understand.
The Shift from Physical to Behavioral Biometrics
Traditional biometrics focused on physiological traits—things that are physically a part of you, like your retina or facial structure. The “new biometrics” often focus on behavioral traits, which are dynamic and tied to your actions. These systems measure patterns rather than static points, creating a high-resolution, continuous identity profile.
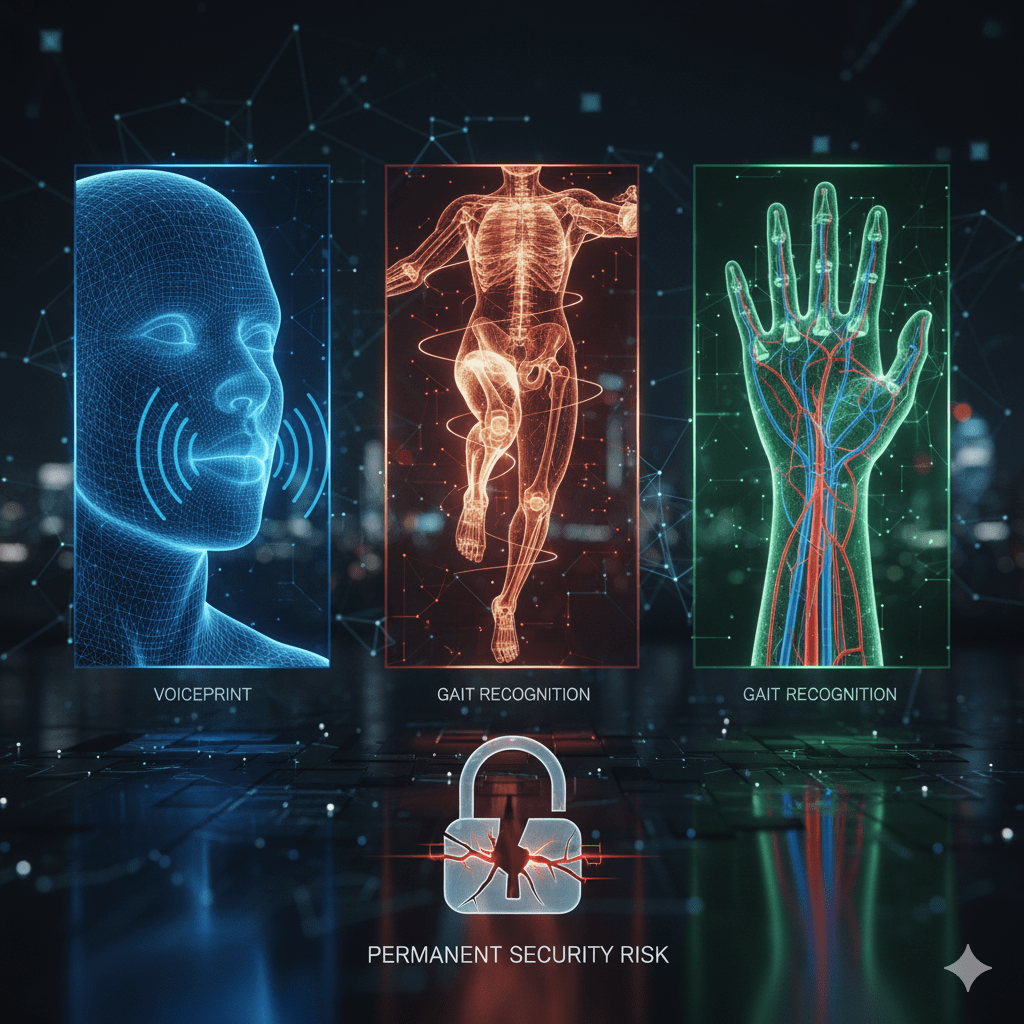
1. Voiceprints: Your Vocal Signature
A voiceprint is not simply a recording of your voice; it is a mathematical model of your unique vocal anatomy and speaking style. When a system (such as a call center’s security system or a smart home device) creates a voiceprint, it analyzes dozens of characteristics:
- Pitch and Tone: The fundamental frequency of your vocal cords.
- Tempo and Rhythm: Your speech patterns and speed.
- Vocal Tract Shape: The unique dimensions of your mouth and throat that influence resonance.
These traits are converted into a unique digital signature: the voiceprint. This can be used for authentication. Voice biometrics are increasingly used in banking and customer service because they offer a seamless, remote way to confirm identity. You don’t have to touch a screen or remember a password; your voice is the key.
2. Gait Recognition: Identifying You by the Way You Walk
Gait recognition is perhaps the most advanced and unnerving of the new biometrics. It operates on the premise that your manner of walking — your gait — is as unique as your fingerprint. This is not simply a matter of speed; it is the complex, repeatable pattern of your entire body in motion.
High-definition cameras, often combined with advanced computer vision and artificial intelligence (AI), analyze features such as:
- Stride Length and Width: The distance and lateral separation of your steps.
- Joint Rotation: The precise angle and timing of your hips, knees, and ankles.
- Center of Mass Dynamics: The subtle way your body weight shifts with each step.
Unlike fingerprints or facial recognition, gait recognition is unobtrusive and works at a distance. It allows security systems to identify a person even if their face is obscured or they are walking through a crowded public space. This capability makes it an incredibly powerful tool for surveillance and access control in large, open environments like airports or stadiums.
The Inviolable Risk: Why a Breach of Biometrics is Permanent
While these new methods are highly secure against typical hacking (you cannot guess a voiceprint), they carry a massive, fundamental privacy risk that traditional passwords do not: permanence.
If your password is stolen, you change it. If your voiceprint or your gait pattern is stolen, you cannot change your throat shape or your skeletal structure. Once compromised, this unique, lifelong identifier is permanently exposed. Since biometric data is often stored centrally in large databases, a single security breach can lead to the irreversible compromise of millions of identities.
This creates the risk of Function Creep: data collected for one legitimate purpose (like quickly authenticating a bank call) being later used for unintended purposes (like mass surveillance or insurance rate calculation based on behavioral patterns).
Protecting Your Unique Data
Given that you cannot “reset” your biology, protecting this data requires both technical vigilance and legislative awareness:
- Demand Transparency: When a company or service asks for a biometric input (voice, face, vein pattern), always demand a clear, written explanation of where the data will be stored and if the raw data is kept or if it is converted into an irreversible mathematical template (a much safer process).
- Use Device-Side Verification: Whenever possible, use biometric systems that perform authentication on your local device (like your smartphone) and only send a digital confirmation token to the server. This prevents your raw voice or gait data from ever leaving your device and being stored in a vulnerable centralized database.
- Support Strong Biometric Laws: Privacy regulations like GDPR in Europe and state-level laws in the US (such as Illinois’ Biometric Information Privacy Act, or BIPA) are crucial. These laws often require specific, written consent before collection and impose strict rules on data retention and destruction. As a consumer, advocating for and supporting strong regulatory frameworks is the best long-term defense against misuse.
The convenience of using your unique biological traits as your password is appealing, but we must ensure that the very data that makes us unique does not become the tool that compromises our most basic privacy rights.
Here’s an interesting YouTube video to helo you learn more about the security implications of advanced biometric systems by watching this detailed breakdown of how they work and the threats they face: Biometrics & Security: Privacy, Deepfakes, & Cyber Threats.